I don’t know how this myth came to be, perhaps it comes from the belief that macOS doesn’t need antiviruses or that there is less news about vulnerabilities in macOS. Whatever the myth about the infallible security of macOS is based on, below you will find out about several facts that are supposed to make you change your mind.
Let’s start with the Pwn2Own 2018 security conference. Pwn2Own is an annual hacking competition held since 2007. White hackers from all over the world are challenged to exploit operating systems, browsers with previously unknown vulnerabilities, escape the environment, etc.
As you can guess one of the challenges of the contest was to hack macOS and they successfully handled it. Two teams of security researchers performed a successful attack on Safari and macOS.
On the second day of the competition, the group from Ret2 Systems demonstrated a chain of exploits for Safari after a successful attack from the fourth attempt. A team of security experts from MWR Labs proved to be even more effective by escaping the Safari sandbox and used a heap buffer overflow in Safari and an uninitialized stack variable in macOS to execute arbitrary code.
Let me remind you that executing arbitrary code allows you to gain full access to a device. MWR Labs earned $55,000 for a Safari sandbox escape. Bu the world’s largest intelligence agencies have a lot more resources and security experts at their disposal.
For instance, Chinese hackers have always managed to become one of the top performing groups at the global security competition. At Pwn2Own 2017 the Chinese Qihoo360 team hacked the Safari browser and escalated privileges to root on macOS. But in the spring of 2018 the Chinese government forbade their IT specialists to take part in international competitions out of national security concerns.
So if before Chinese experts’ discoveries and talent demonstrated at global security conferences served the common good, now their skills will be used in the interests of China’s nationals security. If the Chinese government deems that watching you will serve the interests of its country, these talented security team’s knowledge will be used against you.
The original information about Pwn2Own 2018 is available at thise link.
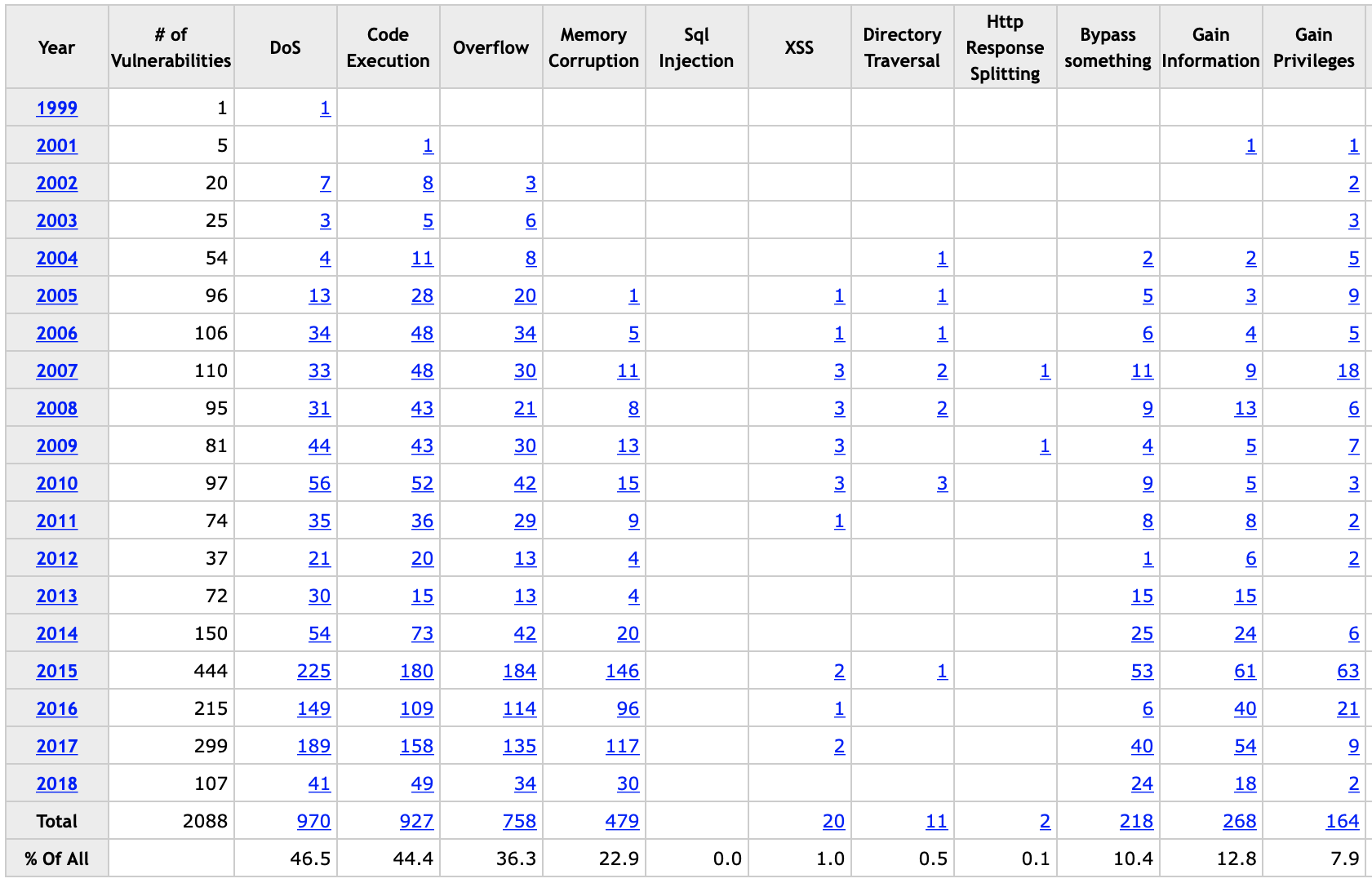
However the results of the white-hat hacking contest are not the only data I want to share with you. Here is the link to the website CVE Detais that publishes the information about vulnerabilities in products, and you can see the statistics on how many vulnerabilities have been found in Safari over a certain period of time.
At the time this material was being prepared for release, 107 vulnerabilities were exposed, but not all flaws are equally dangerous. DoS is an attack that causes a server to overload, and while it’s surely pestering at the least, it’s not fatal unlike Code Execution and Gain Privileges that allow attackers to gain complete access to your Mac computer.
Some time ago I published an article where I made a point of asking you to delete all the applications you don’t use since it increases the risks and vulnerability of your device. Take the iTunes application a lot of users don’t use but don’t delete it either. You can see the statistics on iTunes vulnerabilities by going to the website below:
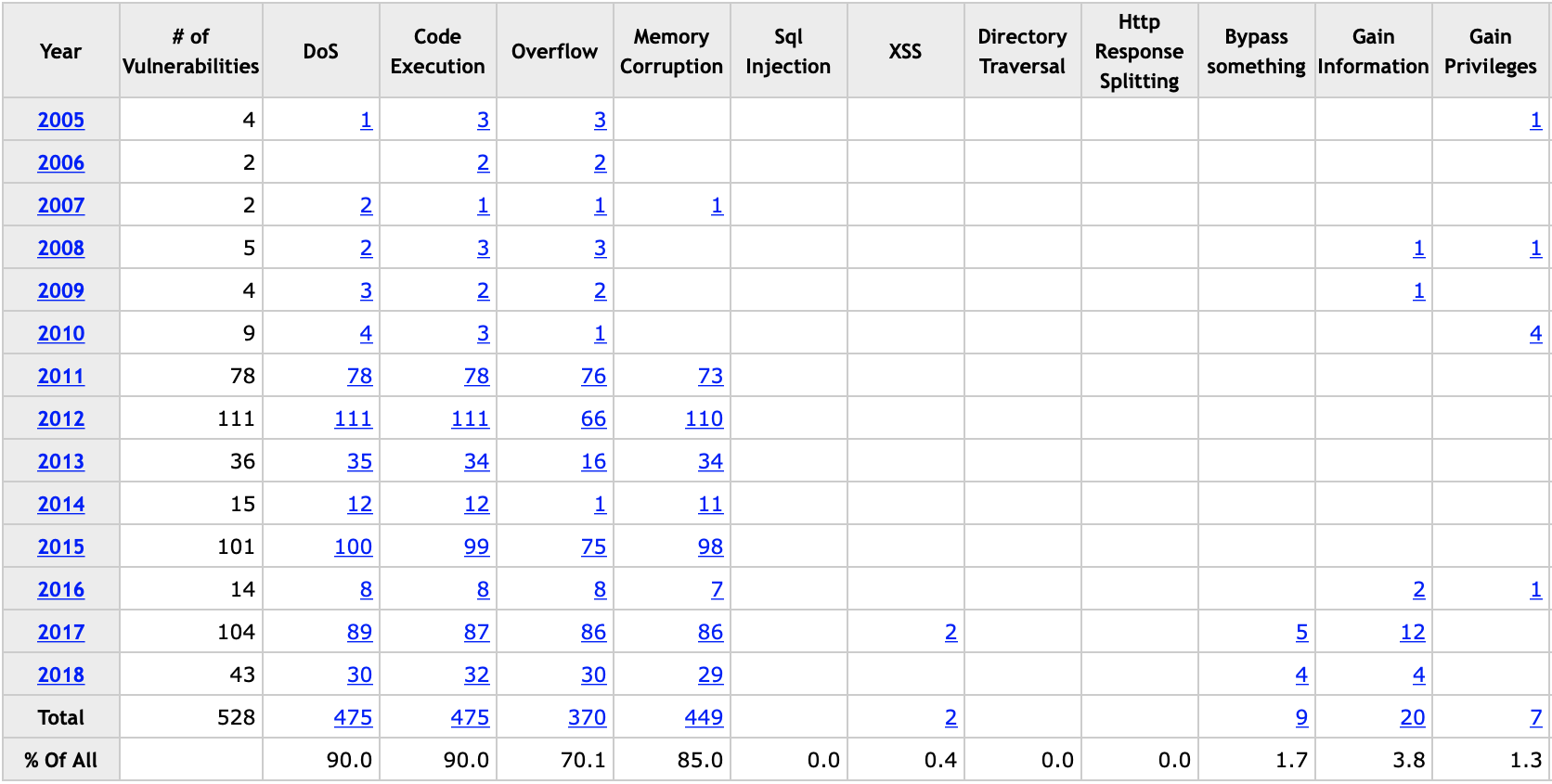
You can see that critically dangerous flaws appear annually and will appear in future. Be aware that this list shows only known vulnerabilities, as a rule, they are already fixed by the software maker and can pose a danger only if you don’t update your system, browser or applications you’ve installed. The flaws used by intelligence agencies are kept in secret, they are not fixed in patches and called 0day vulnerabilities.
If you want to ensure comprehensive security for you, you need to leave behind all myths and illusions. The infallible security of macOS is a myth, and I hope I’ve dispelled it for you. Don’t give in to panic thinking that you can never feel secure, but you have to keep in mind the following thing: hacking macOS is a real threat, and if there’s a chance that an intelligence agency can become interested in you, for instance, you are a politician, journalist or official, you should rethink your security views.
At the same time, as part of this course, you will learn about additional security measures, isolation being the most important of them. Every new level of isolation is a big problem for hackers, and if they escape a standard Safari sandbox because they are ready for it in advance, facing an extra level of isolation will throw them off.
After a hacker successfully defeats Safari’s defenses, after a victim goes to a special link, he has very little time to attempt executing arbitrary code within the system. Often this process is automated and after an escape from the Safari sandbox, the hacker’s decision to exploit the system vulnerability will be met by the limitations of the second level of isolation the intruder didn’t see coming when planning his attack. As a result, the attempt to execute arbitrary code in the system, for instance, by installing RAT, will fail.