I don’t intend the material in this course to be a textbook, and, frankly speaking, I am not going to take you through the entire history and methodology, except for encryption. I can’t help it because first, this is an interesting topic, and second, it’s rather useful as there are still people out there who believe that by substituting letters or words they are securely encrypting their information.
Already in BC the then emperor Gaius Julius Caesar, when writing an important message, used a substitution cipher where he replaced each letter in the plaintext by a different letter some fixed number of positions down the alphabet with a left or right shift of three symbols. If his enemies intercepted the encrypted message, they couldn’t read it, probably seeing it as a foreign language. This method of encryption is named a “Caesar cipher” and belongs to the group of substitution ciphers that rely on symbol replacement.
To illustrate how Caesar cipher works, take a look at the alphabet below. The first line is the alphabet as it is, and the second line – the transformed version with a rotation of three symbols.
a b c d e f g h i j k l m n o p q r s t u v w x y z
x y z a b c d e f g h i j k l m n o p q r s t u v w
For instance, the word anonymitywill be transformed into bopojnjuz.This method of encryption is very easily decrypted by a quick check of all possible combinations. Already in A.D. Caesar cipher was regarded unreliable. It was superseded by more sophisticated substitution methods where letters were replaced with symbols.
Come to think of it, how do you break a cipher where letters are replaced by unknown symbols? Check all possible combinations? But if you replaced popular words with one symbol in your encrypted messages, you left no chance to substitution.
This method was used by Mary Stuart imprisoned in Sheffield Castle in her correspondence with Anthony Babington who conspired and plotted the assassination of Elizabeth I of England. Here’s how their cipher looked like.
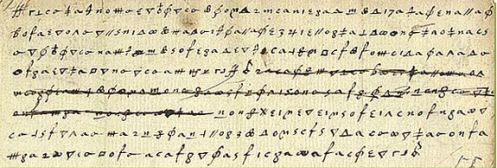
However, Elizabeth’s secret service led by Francis Walsingham intercepted the letter, and her best cryptanalyst Thomas Phelippes easily decrypted it. How did he manage it? He employed frequency analysis.
All letters in a language occur with varying frequencies. For instance, in the Russian language the occurrence of the letter “o” is 11% of all the letters, that of the letter “r” – around 5%, and of the letter “f” – only 0,26%.
Therefore, you simply work out the frequency percentage for the occurrences of the symbols in the text, and it makes it possible to suggest which letter this or that symbol replaces. Then the process requires some time for substitution and testing of the assumptions. That basically sums up what frequency analysis is. It can be applied only to relatively long texts, and the longer the text, the more effective it proves.
Anthony Babington was eventually hanged, drawn and quartered. Maria Stuart was beheaded, and the encryption method that used letter substitution since then has been seen as ineffective. However, the frequency analysis was quickly overcome. It is enough to use several ways of encryption: encrypt one line with one method, another line – with another one, and the frequency analysis will be useless.
Since that time there has been a constant race between devising encryption and cracking ciphers. The most prominent success of cracking encryption algorithms is the breaking of the Enigma machine used by Nazi Germany for protecting its secret wartime communication codes. Enigma is considered a perfect encryption machine at the time that was designed by Germany’s most talented specialists.
But it took just as much talent to break the Enigma Code: an entire team of British cryptologists headed by a young scientist Alan Turing relentlessly worked to crack it. Despite the mystery around Turing, he is said to devise a means for obtaining the key for breaking Enigma. And his breakthrough was prompted by an ordinary Nazi salute that was mandatory for use at the end of every encrypted message.
Alan Turing made the impossible by providing his country with an invaluable advantage in the Second World War. In return he was “rewarded” by a chemical castration homosexuals in Great Britain were subject to at the time. That led Turing to end his life.
Modern algorithms like AES, Twofish, Blowfish significantly differ from substitution or rotation of letters and even from Enigma’s cyphers. Actually they don’t have anything to do with them and are resilient to attacks by guessing or frequency analysis. But they are certainly not immune to one immutable thing – there are still people who want to crack encrypted messages.
Today the existence of such secure data protection tool can’t but bother special agencies interested in gaining access to any information.
Attack vectors against ciphers attempted by special services
There are currently three main attack vectors targeting ciphers on the part of special agencies.
Going through all the possible keys for ciphers. For this purpose data centers are built for breaking encrypted information through key guessing. Trying can get almost any modern cipher cracked; plainly speaking, you can just guess the key (which is logical as if there is a key in place, in theory, sooner or later, it can be guessed). The question is how much capacity and time you have at your disposal.
For instance, one modern computer can check 10, 000 possibilities of keys per second. A data center made up from thousands of computers can try tens of millions of keys per second. Fortunately, to crack a sturdy cipher, it will take a modern data center not one dozen of years to succeed, and, second, it is hard to guess what you could do to make an entire data center take on your encrypted data. Because one day of running a data center costs tens of thousands of dollars.
It is exactly the cost of the resources that makes dictionary-based attacks the main method of defeating encrypted information. This is illustrated by the case involving Brazilian banker Daniel Dantas who was arrested in Rio de Janeiro in July 2008 on charges of financial fraud. During the raid of his apartment the police seized five hard drives with encrypted data. The local experts failed to decrypt the files held on the hardware and turned over the job to the code-breakers at the FBI.
After a year of failed attempts, the FBI representatives returned the disks. To break them, they used dictionary attacks that are explored in detail in this chapter. I don’t know if that tipped the odds for Dantas at the trial, but the access to encrypted information was never obtained. The files were encrypted using TrueCrypt – an encryption program you will learn about as we move further into the course.
In addition to data centers, the development of a quantum computer is on its way, and it is capable of completely changing the modern cryptography. If cryptographers’ estimates prove correct, after such supercomputer is created, any modern encrypted file-hosted volume can be broken quite fast. Some scientists believe that such supercomputer is already invented and runs somewhere in U.S. NSA’s secret labs.
While I was preparing this material, specialized editions broke the news from Microsoft. The software giant is bent on actively developing a quantum computer, and according to the official statements, has quite an optimistic outlook on its current results.
The second attack vector is scientific research of modern algorithms in order to break them. This kind of research requires a lot of money, and such solutions are truly invaluable for special agencies and intelligence services.
Basically, there is a constant tug of war between researchers and special agencies. If researchers crack a protocol earlier or reveal a vulnerability, the world will, most likely, find about it and switch to more secure algorithms. If special agencies succeed first, it will be secretly used for getting access to encrypted information.
Some years ago, a 768-bit RSA key was regarded as an absolutely secure solution and was used by individuals, major companies, governments. However, at the end of 2009 a group of engineers from Japan, Switzerland, the Netherlands and U.S. were able to crack the data encrypted with the encryption key RSA with a key length of 768 bits. The users were recommended to use RSA keys with a length of 1,024 bits.
However, today even 1,024-bit RSA keys are not considered to be secure enough. For instance, users who prefer to set up a personal VPN using our application CrowdShield will be recommended to choose a basic option with a 2,048-bit key and maximum protection with a 4,096-bit key length.
We do not have any accurate information about the resources special agencies may have at their disposal, so the possibility cannot be ruled out. Therefore, CyberYozh security group’s specialists recommend their customers to err on the side of caution and choose extra sturdy solutions. If a 2,048-bit key is seen as secure now, use a 4,096-bit key.
When talking about encryption breaking, we are not looking at such cases when the FBI got into the terrorist’s iPhone and which received extensive media coverage. The FBI just found an alternate method that bypassed iOS’s security mechanisms that destruct all data contents after too many incorrect attempts at logging in to the app. By itself cracking a password of such length is a trifle for experts. As we move further into this course, you will find out how to bypass the security systems of mobile devices.
The third attack vector is the collaboration with the developers of devices, applications, encryption algorithms to weaken encryption and install backdoors.
Defeating a properly encrypted file-hosted volume is often out of special agencies’ reach, at least accomplishing that over the period of a human life. However, they try to cooperate with companies that develop encryption tools so that the latter can leave them loopholes for decryption or make the algorithms being used vulnerable.
NSA is especially persistent in this department. Edward Snowden’s disclosures made it known to the public that an American developer of encryption and computer security products RSA Security arranged a 10 million dollars contract with NSA for installing a backdoor in its application. For this money RSA offered their customers a knowingly flawed random number generator Dual EC DRBG.
This weakness allowed the U.S. special agencies to easily decrypt traffic and files. RSA Security’s solutions were used by leading international companies such as Adobe, Oracle, Sony.
We don’t know what other backdoors are incorporated in encryption algorithms, but one can say for sure that information decryption is one of the top priorities of special agencies. Highly qualified professionals are continually working on it, and governments are investing huge amounts of money. And their biggest effort is concentrated around breaching SSL protocols, security technology 4G and VPN.
But enough theory – let’s move on to practice. In the next chapters of this paragraph you will learn how to securely encrypt your data.