A weak password can negate all your further efforts to ensure the protection of your private data. For this reason, you find this chapter at the beginning of this course as its importance can’t be overestimated.
First, take this test to check how strong your current password is.
Using secure passwords is not as simple as it may appear on the surface. And though most users know the basics of creating a strong password, when it comes to using them on a day-to-day basis, they forget about them preferring a common and easy-to-remember password over a secure one.
In the chapter showing the mistakes that hackers make which can cause their downfall, I told you about one of FBI’s most wanted hackers Jeremy Hammond was caught because of a ridiculously weak password to his encrypted hard drive. Ross Ulbricht, the founder of the drugs marketplace Silk Road, got himself arrested by the FBI agents when they grabbed his computer when it was on, totally unencrypted with a notepad file full of all his passwords. In this chapter, you will find out how to create secure passwords and ensure their safe storing.
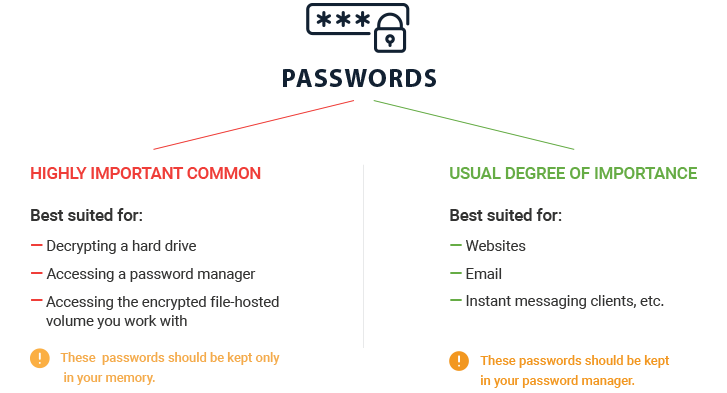
I assume all passwords can be categorized into two groups by how important they are: passwords with a high level of importance and regular level of importance.
Where would you use passwords of high importance? For websites that you consider especially important, encrypted file-hosted volumes or applications. I use four high-importance passwords. The first three are the passwords used for decrypting the hard drive and the information on it as well as for decrypting the data on encrypted external hard drives (the third password provides access to the “secret compartment”). The fourth password is the password to the rest of the passwords in the password manager KeePass we are going to talk about in this chapter.
Passwords of high importance should be kept only in your mind and be as difficult as possible. Passwords with a high level of importance shouldn’t be written down anywhere.
Don’t feel confused about some terms you haven’t yet grasped: if you have never encrypted your hard drives, if you don’t understand what an encrypted file-hosted volume’s “hidden compartment” is and you don’t use a password manager. As you walk through this course, you will learn how to do it all and keep your data safe and secure.
Tip
The most important passwords should be as secure as possible and kept only in your head.Passwords with a regular level of importance refer to all the rest passwords you use, for instance, passwords to social network accounts, email, websites, instant messaging clients. However, you are the one who determines the importance of a password for yourself. Perhaps you are discussing a political coup in your country by email and your country happens to be North Korea where people are executed for this by getting blown up with an explosive up their rectum.
Now let’s look at the right ways to work with your passwords. All the information on your computer should be encrypted and to decipher it, you need to enter a password. This is a password of high importance, therefore you are keeping in only in your head.
You’ve decrypted your hard drive, all your passwords of regular importance are stored in an encrypted file of the password manager’s keys. To decrypt this file, also use a password with a high level of importance.
I have to mention a practically unbreakable password. I used “practically” since in theory it is possible to crack any password sooner or later, but it may take at least a thousand years.
The requirements for a strong password are as follows:
- Avoid words or phrases. The password atxi1387_1 is always more secure than taxi1387_1.
- Avoid dates, especially those of personal or historical significance.
- Your password should be at least 20 characters. This is not such a long password as it may appear. For instance, the word “uncharacteristically” has 20 characters.
- Your password should have uppercase and lowcase letters, more than one number, symbols.
- Your password shouldn’t contain the information related to you, home address, pets’ names, date of birth, phone number, your favorite soccer team’s name.
To make a strong password that would conform to all the requirements above, yet would be as simple for remembering as possible is a tough task. So take a pen and paper, read my story of creating a password and then try making a few strong passwords.
How I came up with a password
First, I made up a word that can’t be known by either Google or a dictionary. The word I came up with was “dortarulin”. To make it more difficult, I replaced i for 1 and got “dortarul1n”. Next, I added upper-case letters. Very often users capitalize the first letter of the word or the first and last letter both (ExamplE) or every other one (ExAmPlE). In my view, these are too obvious passwords so I altered it to “dortArul1N” since there is no logic to how the uppercase and lowercase letters are strung together.
I don’t recommend using keyboard layouts when creating a password. For instance, when you are using an English keyboard layout while entering your word in Russian with Cyrillic letters (Ghbdtn – “Hello”). There are a few reasons for avoiding it: first, a brute-force attack system is aware of this trick. Second, if you have to enter a password on a keyboard that doesn’t have a Cyrillic layout, what will you do? I recommend you use only Latin letters when making your password.
Finally, my password lacked symbols (;.%^&) and wasn’t as long as 20 characters yet. Then I decided to add an equation, 4х(16+y)=? and got dortArul1N_4х(16+x)=?. This password has a total of 21 characters long rendering it very secure.
How I learned my password
When you make a password independently, it’s not so hard to learn it. Personally, on my first day I scribbled it many times on paper, then I wrote it down on paper every morning over a week. In a week I had no difficulty in remembering and reproducing it on paper.
You’ll have to create and learn a few difficult passwords, there’s no way around it. Remember that making and learning one password and start using it everywhere is a bad way to ensure your safety that gives you absolutely zero protection.
Using the same password for several websites or applications or modifying it is quite common. Indeed, this is convenient and if you modify your password – relatively safe. What do I mean by modification? For instance, you are using a passphrase Kireev1000 for one website and Kireev2000 – for another one. If somebody obtains access to your password Kireev1000, he won’t be able to use it to access the website with the Kireev2000 password. However, on the other hand, if this person attempts a brute-force attack on your password using specialized software, he will succeed.
Unfortunately, many people don’t just use a weak password but also the same password for several resources. Some websites and programs are designed especially for collecting logins and passwords. Suppose, you’ve come across an interesting website and want to register on it. When you register, the website will ask you for your current email address and then ask you enter a password, but you are unaware that this site belongs to perpetrators, and all the data you give are sent directly to them. They automatically check if your login and password can be used to access the accounts of your social networks, popular services, they check if they can use the password you’ve just given to access your email. If they succeed, the perpetrators will start using your accounts and email address to send spam or sell them off in the underground market.
Tip
Every password should be unique, passwords shouldn’t resemble each other. Never use the same password for two websites/services/applications.Again, using one and the same password or a single password with slight changes is a glaring mistake that seriously endangers your online security and privacy. Using simple passwords is even worse. Just as you don’t put up a building without building a strong foundation first, your online security and privacy should start with strong passwords.
Regular changing of passwords
I am wrapping up this chapter by mentioning the importance of regular changing of passwords. Unfortunately, since this is a bit of a hassle, users tend to either forget about it or feel too lazy to actually do it, so they just overlook it.
Some users would argue that there is no need to change your passwords as they don’t really expire. However, in reality, changing your passwords regularly protects you from “hidden” leaks of data that often occur at organizations. At the end of the part, you will find plenty of examples of data leaks that have become available to the public. However, we know only about the hacker attacks when malicious intruders leaked data online. But we also know that intelligence agencies of different countries of the world are involved in data hacking, and they are very unlikely to reveal their successes, hacks and leaks.
Therefore, I recommend changing all your passwords every three months. If it’s too much trouble for you, change your passwords at least every six months. If you perform a regular changing of your passwords, you completely change all the passwords you use.