History of TrueCrypt
There’s hardly any information security expert left who hasn’t used the TrueCrypt software. Our reverence for TrueCrypt resembles that for the Holy Sepulcher for Christians and Caaba for Muslims. All because TrueCrypt is an almost perfect application for encryption of folders and files.
The first version of the software dates back to 2004, and at the time it was basically the only open-source on-the-fly encryption application.
What does “on-the-fly” mean? Common encryption programs, before you start working with encrypted files, require that you first decrypt a file or folder after performing a series of actions, create an encrypted copy of the file or folder and delete the unencrypted original copy. TrueCrypt allowed to create an encrypted folder entering a password in the application and work with the encrypted file, encrypting and decrypting data automatically, or “on-the-fly”.
From 2004 through 2014 TrueCrypt was regularly updated. Some functions were soon dropped: for instance, floppy disk support as this format became obsolete. Some encryption protocols became unavailable. The advances in computer software spurred and enhanced the technologies designed for defeating encryption methods. As a result, a range of protocols were no longer seen as secure. Thus the 7th version of TrueCrypt no longer has the encryption algorithms with the 64-bit block ciphers (Triple DES, Blowfish, CAST5).
For 10 years TrueCrypt evolved and turned into fundamental data protection software. All this time the names of the developers remained a mystery spurring the abundant rumors that special agencies were connected to the development of the application. Some speculated that the software had been created by the FBI, others assumed that even if the FBI didn’t have anything to do with its development, it must have back doors in it.
The popularity of TrueCrypt grew until in the spring of 2014 the Internet community was stunned by the news that on May 28th, 2014 TrueCrypt had been shut down. The reasons for the abandonment of the project are still unknown to date. The developers themselves announced on its official website that using TrueCrypt was no longer safe and encouraged users to switch to Bitlocker - the encryption program that has always been looked down upon by them.
Different versions and assumptions abound as to why TrueCrypt was discontinued. According to one of them, its developers were coerced by the special agencies; an alternative version says that they were hired by Microsoft – the move that would explain why they advertised Bitlocker. Perhaps, the authors behind the software were no longer interested in supporting a project that didn’t generate revenue. Or they found a critical bug that couldn’t be corrected.
The Internet community became engulfed into a debate around TrueCrypt’s security until by the beginning of April, 2015 a security audit of TrueCrypt, whose crowdfunding campaign collected over 60 000 USD in donations, was completed. It revealed no vulnerabilities or serious flaws in the architecture and concluded that TrueCrypt is a well-designed cryptographic program.
Source https://opencryptoaudit.org/reports/TrueCrypt_Phase_II_NCC_OCAP_final.pdf
Version TrueCrypt: 7.1 а.
Audit Year: 2015.
We believe that TrueCrypt 7.1 is reliable enough and that the shutdown of the project wasn’t connected with the presumable breach in its security.
However, the latest version of the application (7.2) proved to be neither secure nor completely functional. At least, that’s what the developers themselves warned users about, the opinion shared by many experts. Therefore we recommend using the latest consistently reliable version - TrueCrypt 7.1a.
Unprovability of encrypted file-hosted volume
TrueCrypt boasts a host of advantages, one of them having to do with the ability of a TrueCrypt encrypted file-hosted volume to remain unidentified. Even if malicious intruders gain unauthorized access to your hard drive, point the encrypted volume out and say, “this is an encrypted file-hosted volume”, you can confidently respond that this is some unknown file. It is impossible to prove the reverse.
Well, of course, your finger could “accidentally” get caught in the door, and then you won’t just recognize this file as an encrypted volume but will also remember the password to it. You can protect yourself against it, and you will find out how in the chapter devoted to anti-computer forensics. Just remember that it is impossible to prove the existence of an encrypted volume by examining a file.
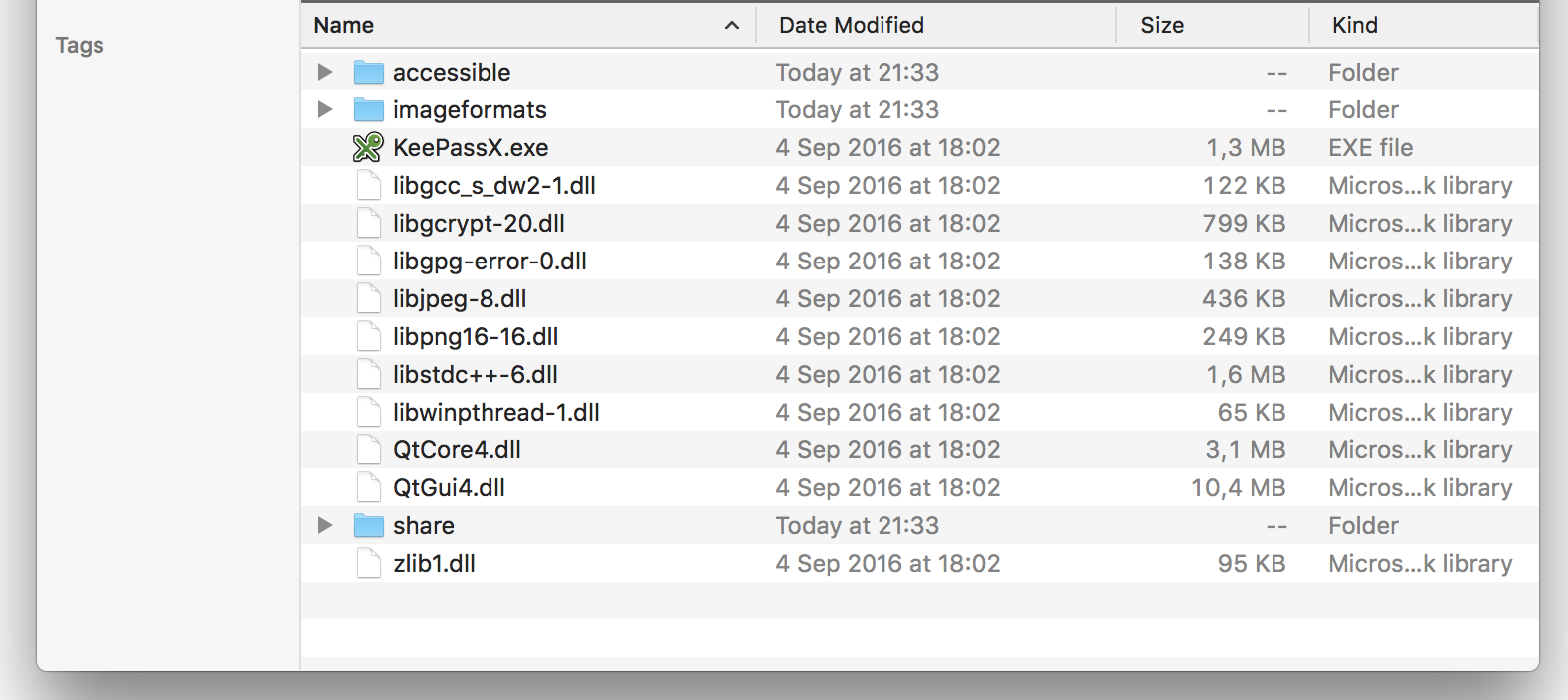
With that in mind, we recommend you name your encrypted file-hosted volumes neutrally, disguise them as program files. For instance, suppose we have a folder with the password manager KeePassX and we see some files with the extension *.dll. When you create an encrypted volume, name it LsQN7.dll and put it into this folder. In this case only you will know that LsQN7.dll is actually an encrypted file-hosted volume.
Before I created an encrypted volume.
After I created the encrypted volume and put it in the folder KeePassX folder.
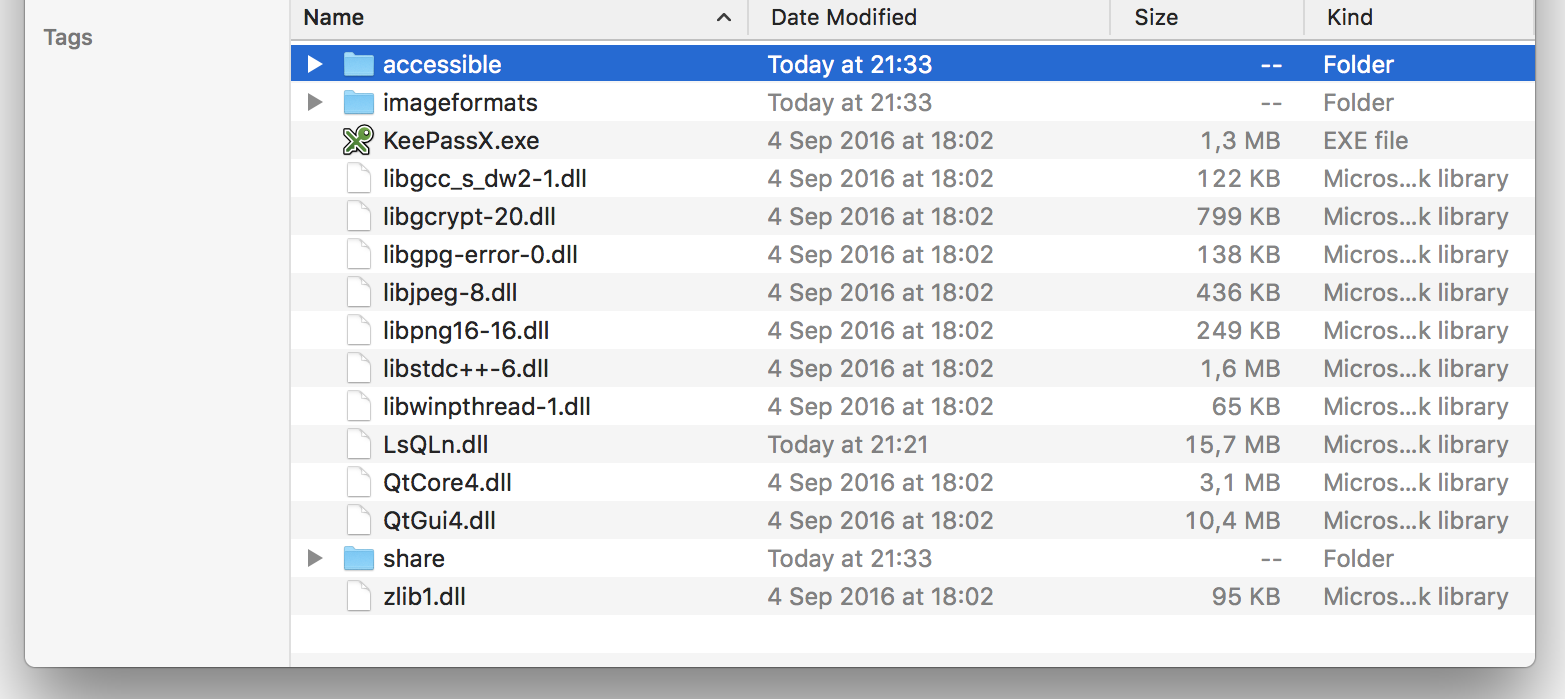
Can you spot the differences? The date, right? You will find out how to change dates in the part of the course devoted to disguising encrypted file-hosted volumes. But don’t rush to create an encrypted volume now…
We have mentioned above that an encrypted volume doesn’t differ from the file it disguises itself as on the outside, but there are definite differences beneath the surface. For instance, the files *.mpg *.jpg *.dll *.avi *.mp3 and many others have a binary file header. Using the file’s header, one can infer that the contents of the file doesn’t belong to the file of the particular type. There are also the so-called untyped binary files. The most common of them is a *.dat file. Such files don’t have a binary file header and their contents can’t reveal anything to identify them by. This type of files is your best choice as a disguise for an encrypted file-hosted volume.CyberYozh security group expert
Tip
Choose a name for your encrypted file-hosted volume that wouldn’t give this encrypted volume away. Use the *.dat extension for encrypted volumes and place them in a folder with other files having the *.dat extension.Be aware that the existence of TrueCrypt on your desktop can provoke malicious intruders as a red rag to a bull. They would immediately look for encrypted volumes, demand passwords, attribute all kinds of criminal intent to you, ranging from drugs dealing to supporting international terrorism.