There are situations when you need to instantly destroy your encrypted file-hosted volume with sensitive information, and in this chapter you will find out how to do it. You could have a backup copy to restore your volume later, or the situation simply requires an emergency destruction of data to an unrecoverable state. So, you have several options at your disposal.
A simple solution would be to copy the key file to a microSD card and physically destroy it when necessary. Do you remember where you saved your key file (when we created an encrypted file-hosted volume and added a key file in addition to the password)? You probably saved it to the hard drive, and now you just have to transfer it to a microSD and delete the original file using the safe data removal technique. We are closely looking at safe data deletion in a separate chapter.
If you securely destroy a microSD card, for instance, by burning it, there is practically no chance of restoring your data in an encrypted file-hosted volume. Unless, of course, you stashed a backup copy of the key file in the cloud or alternate storage.
The downside to this option would be the price tag of a microSD and the risk it won’t be deleted entirely. Also, the encrypted file-hosted volume doesn’t get damaged in any way and can be found by perpetrators. The advantage of this method lies in its simplicity: you go to the nearest store, buy a microSD and then transfer the key file to it. As you see, it’s no rocket science.
Your second option is Panic Button. This is a specialized application for emergency data erasure and notification about unauthorized access to your device. But in this case we specifically want emergency data erasure.
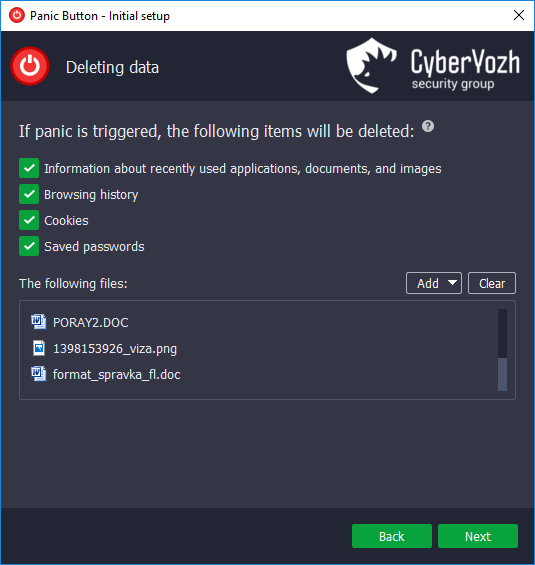
Download and install the application. Upon the initial setup of Panic Button, in the window “Data deletion” add the encrypted file-hosted volume and other files you wish to destroy to the list of the files for removal.
If you receive an alert, Panic Button can be activated by a combination of keys and at the press of the “Panic” button. After you activate “Panic”, all the selected data will be securely destroyed, RAM – cleared, and your computer – turned off.
The key advantage of Panic Button is the ability to set off in logic bomb mode. Even if perpetrators obtain physical access to your computer, Panic Button will be activated independently and destroy your encrypted file-hosted volume.
Panic Button also offers the cryptocrash system that allows to destroy encrypted file-hosted volumes of dozens and even hundreds of GB in size just in seconds. Panic Button destroys the critical elements of an encrypted file-hosted volume rendering it completely unusable and removes the rest of it in standard mode.
Your third option is to get a hard drive destruction system. Similar solutions are available for sale, for instance, Samurai systems. Such device can be embedded in a computer, and it will destroy all the information on the hard drive. As a rule, such systems subject a hard drive to a high-intensity magnetic field, sometimes physical damage is applied to it simultaneously.
Pros: such system can be launched with a remote control unit from a distance of up to 1000 meters. As a rule, similar systems offer SMS activation, and you can destroy your hard drive just by sending an SMS to the phone number you indicated before. Some models are set off if an intruder attempts to gain physical access to your hard drive or to put the CPU in horizontal position (in case of unauthorized transportation).
Cons: the price tag, on average such system costs around $500-1000. The system destroys the whole hard drive rendering it irrecoverable. It is suited only for desktop computers of standard sizes. Though I have seen similar solutions for laptops packaged in the form of a suitcase, they are quite cumbersome to use on a day-to-day basis.
