Many expected that the first chapter and advice in the section on software would be to update the programs, download them from reliable sources, conduct an audit of rights and Internet traffic; all of this is certainly important and we will definitely do this as part of setting up an integrated security, but we will start with an audit of installed applications.
What does it mean? This means that you need to open the list of applications and delete all the programs that you do not use. This is a universal rule, which applies to computers, phones, and tablets.
Often after buying a new smartphone a lot of applications are being downloaded to it, many of which will never be used. The situation is even worse with old devices, where over the years dozens of programs can be installed. All of that must be removed.
Having removed unused programs, revise the list again and remove applications that you use very rarely or plan to use in the future. You should not have programs “just in case”. If you need them one day, you can always install ones.
Especially, I advise you to delete bank applications. Some of their applications have the functionality and rights that any warrior would envy. For example, a “green” bank app can continuously collect information about all applications used by the owner, scan the system, read and send text messages, receive images from both cameras and view contacts without noticing the owner. The application also has access to browser history, can listen to calls, change device settings and constantly collect geolocation data.
Advice
If your security is really important for you, you should never install bank apps on your devices.Another common misconception is the belief in the security of the manufacturer's applications, especially when it comes to such giants as Microsoft, Google and Apple. When I conducted a security audit of my girlfriend’s iPhone, I found many pre-installed applications she had never used, such as mail, roulette, books, which I deleted for sure. A similar situation was found on her MacBook.
My girlfriend thought that Apple applications were beyond suspicion and couldn’t make any harm, although only a couple of months earlier in the official Apple GarageBand application there was revealed a serious vulnerability. It allowed the malefactor to create a special file that, when opened on the victim’s computer, allowed them to execute arbitrary code, in other words, to do everything the malefactor wanted to do, like to steal some data or install software for cyber espionage.
Right you are to pull me up, as opening a file is already dangerous, you need to be careful. The problem is that it was absolutely harmless in terms of the macOS security system and Virustotal .band file used in the GarageBand app. In the sandbox you can view a picture or a document, but you will not be able to work there with GarageBand.
I often meet installed applications for controlling a computer remotely, for example TeamViewer. Usually they are installed to receive remote technical support and they are not removed after that ... although the appearance of a vulnerability for such an application will give full access to the victim's device. In the same TeamViewer there have already been revealed some critical vulnerabilities.
Remember: each installed application potentially increases the vulnerability of your device. Reducing applications to a minimum is an important step in comprehensive device security configuration.
Advice
Audit devices and remove unnecessary and rarely used programs.How to delete programs?
This is not exactly the topic of this course, if you do not know how to remove programs from your device, you should start with basic courses or contact a search engine.
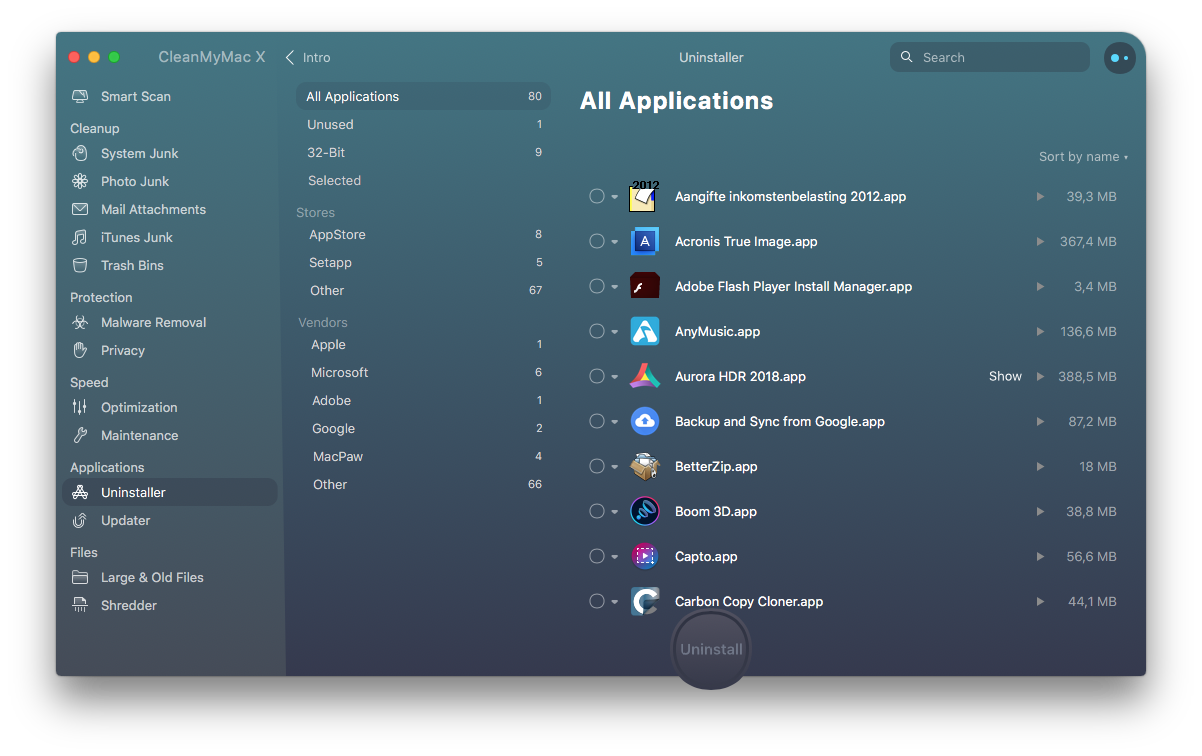
For convenience, you can use CCleaner app in Windows, CleanMyMac in macOS, UnApp in Android.