Whatever reliable method of information transmission you are using, if you want to stay sufficiently secured, it is better to use several ways of data transmission disrupting its continuity. For instance, if you need to send a combination of a password and login, you should use one communication channel to send your login and choose a different one when sending a password.
This is where one-time-use notes come into play. Privnote is one of the most popular services of this kind to date.
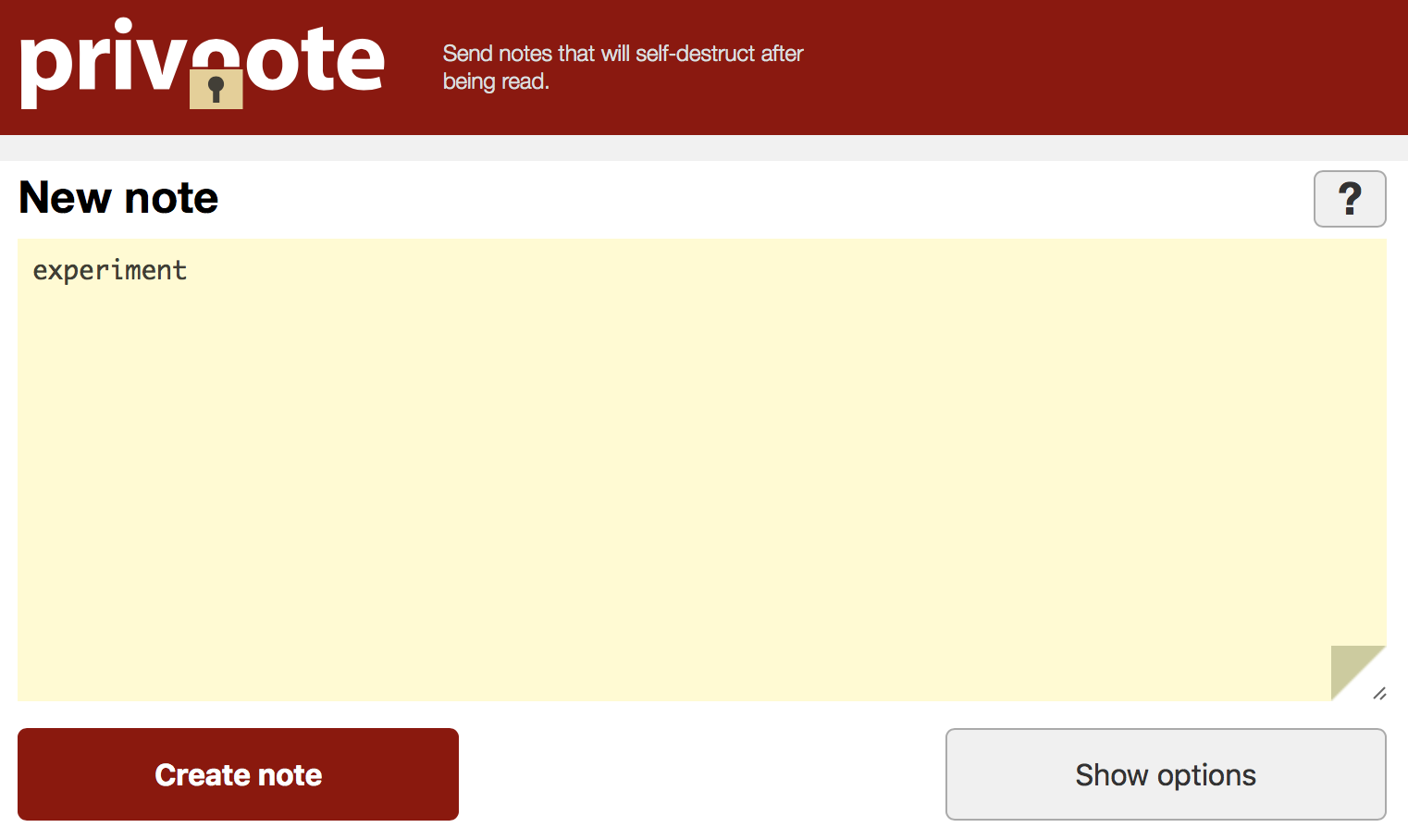
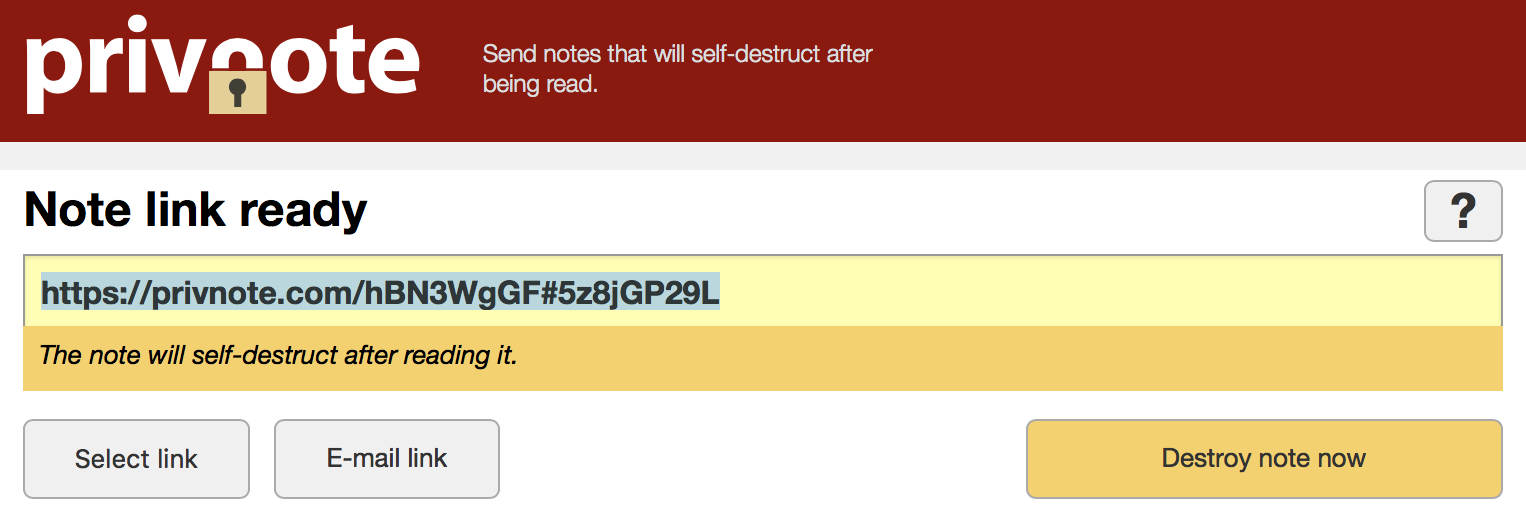
Privnote allows users to send one-time-use notes that self-destruct after being read. Using Privnote is very easy: you create a note, receive a link for one-time reading and send it to the recipient.
Though Privnote is an old and recognized service, we will not trust it with all the information we have, its sole task is to break the information chain. Thus Privnote is kept out of the information chain, also removing your message from the correspondence.
Take a closer look at the link, it consists of the address of the website/note’s identifier#user’s decryption key. A user’s decryption key is stored in the link in the form of anchor. Anchor is the part of URL that follows the crosshatch # character in the link and is never sent to the server (RFC by URL http://www.faqs.org/rfcs/rfc1808.html, Section 2.4.1). Browser doesn’t send this part of the link, and server doesn’t receive it, as a result, the decryption key is kept on user’s computer until he or she wishes otherwise. In theory, Privnote’s owners are unable to decrypt your note.
Let me show how Privnote can be used in more detail. Suppose, you want to send a person’s phone number and some information without leaving any traces of this data in your correspondence.
You send the recipient the following “Don’t forget to call me tomorrow https://privnote.com/9qn1wkwq#Kuz62vdzL Ivan.”
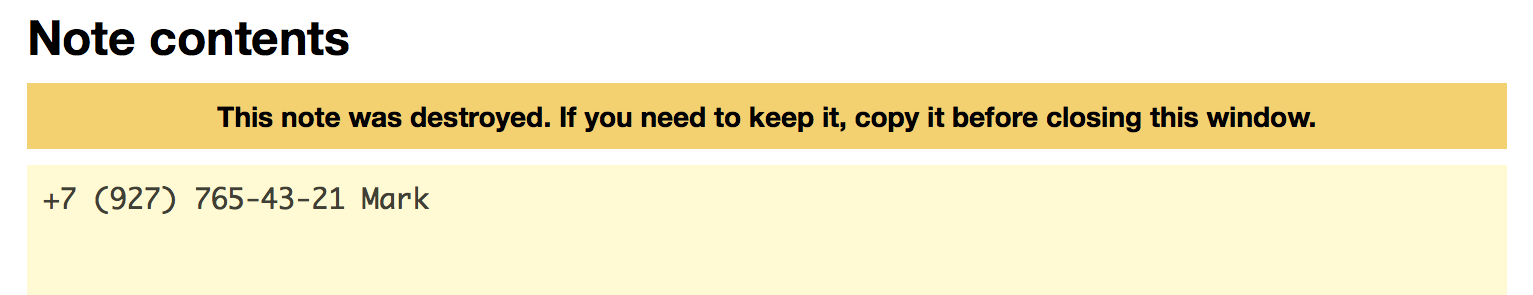
When clicking the link, the recipient sees the note.
Or suppose, you need to send confidential data to enable connection to the server. You can use the instant messaging service Telegram to send the port, IP address and login and Privnote – to send the password.
You send the following “111.11.111.111 port 17893 login root password https://privnote.com/9qn1wkwq#Kuz62vdzL".
Even if someone else snoops on your correspondence, it will be revealed at once since the recipient won’t be able to access the one-time-use note that has been read before.
If malicious intruders access your correspondence, for instance, if your device gets stolen, they won’t be able to recover its content fully as a Privnote note self-destructs immediately after being read.
Privnote is very popular with blackmailers since the evidence and incriminating material self-destruct after being read. The perpetrators would use URL shortening services like Bitly to make sure the correspondence doesn’t contain even the links to Privnote.
The shortened link is afterward removed through the service where it was created, and as a result, the victim is left only with an ineffective link of the URL shortening service. There is very little chance that police will consider this kind of evidence.
Tip
Disrupt the continuity of information using one-time-use notes by Privnote or analogous services.For added security, Privnote allows you to protect your notes with a password by enabling this option in the settings when you create your message. Use an alternate method to transmit the password to your note, for instance, by phone. If you are sending it along with the rest of the message, you basically render your password useless. Make sure to add this tool to the bookmarks of your browser and start using it.
In conclusion, I’d like to draw your attention to this important point. When receiving a Privnote, few users expect a pitfall, but you should be vigilant at all times. Recently a fake Privnote website was used to carry out a phishing attack. The legitimate website is privnote.com, but the victim got a link to the website privnote.cc created by scammers.
A scammer sent a message to his victims on Telegram, mainly to the sellers of various Deep Web forums and e-currency and cryptocurrency exchange services, negotiated with them, agreed on a deal and sent the payment information using a fake Privnote website.
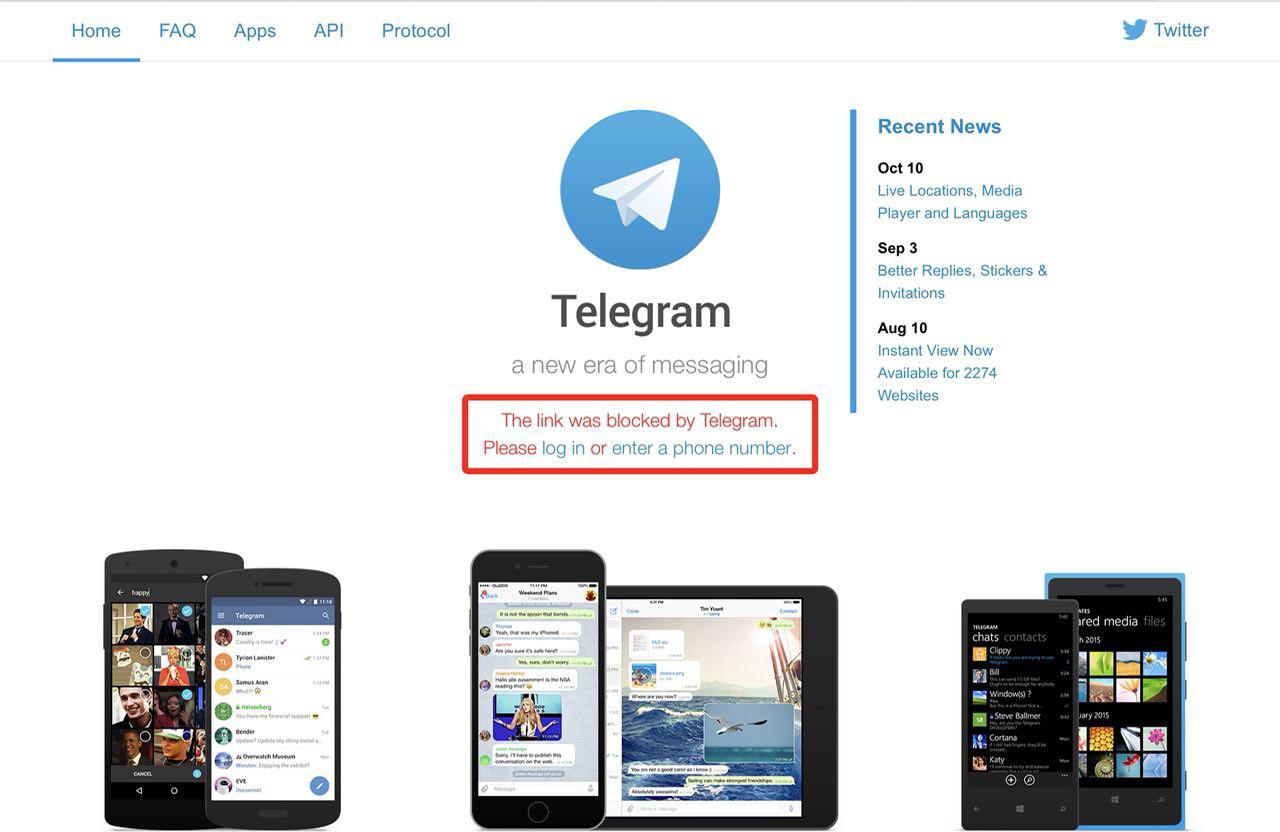
When a victim used the link, the fake Privnote website didn’t look any different than its legitimate counterpart.
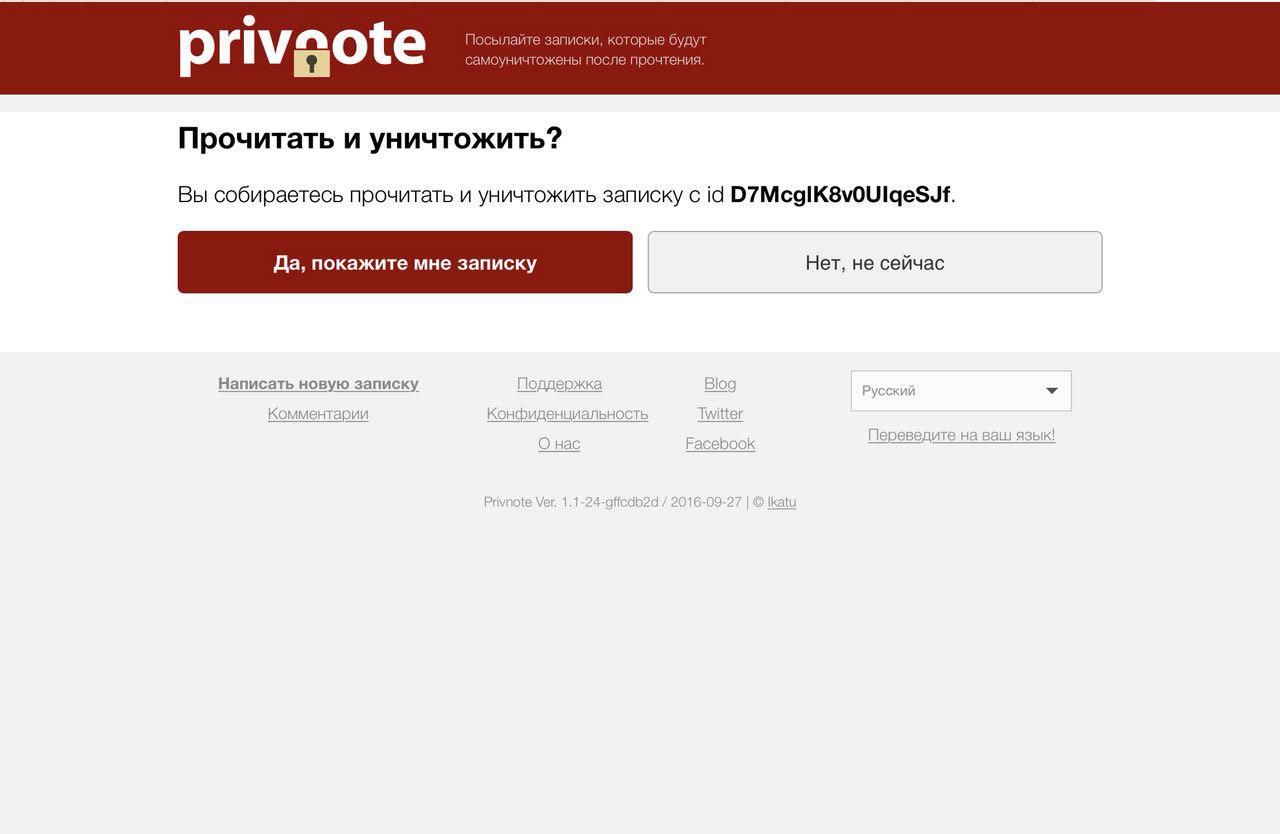
However, when attempting to read the message, the victim received the information that the link is blocked by Telegram, and that in order to read the message, he or she needs to log in to the account. If the victim entered their account details, they instantly leaked to the scammer.
The scammer went on to enter the victim’s Telegram account and started accepting money from customers.