This chapter will show you how to see if your messages in instant messaging applications are read. We used this method on a popular Russian social network by creating a provocative personal message that is supposed to be read by moderators. They did, and we actually saw that our messages are read. If you want to check if your correspondence is read by your spouse, hacker or boss, this method will come handy.
This method comes down to creating a link-trap that will be added to your message. The trap will be set up using a one-time-use note Privnote.
You have probably read about Privnote in our previous chapter. This is an extremely handy service that allows users to disrupt information chain. But now you will learn how to use it to trap snoopers.
Privnote allows users to send notes that self-destruct after being read – everyone knows about this core functionality, however, few know that Privnote also allows you to receive an email notification of the note being read.
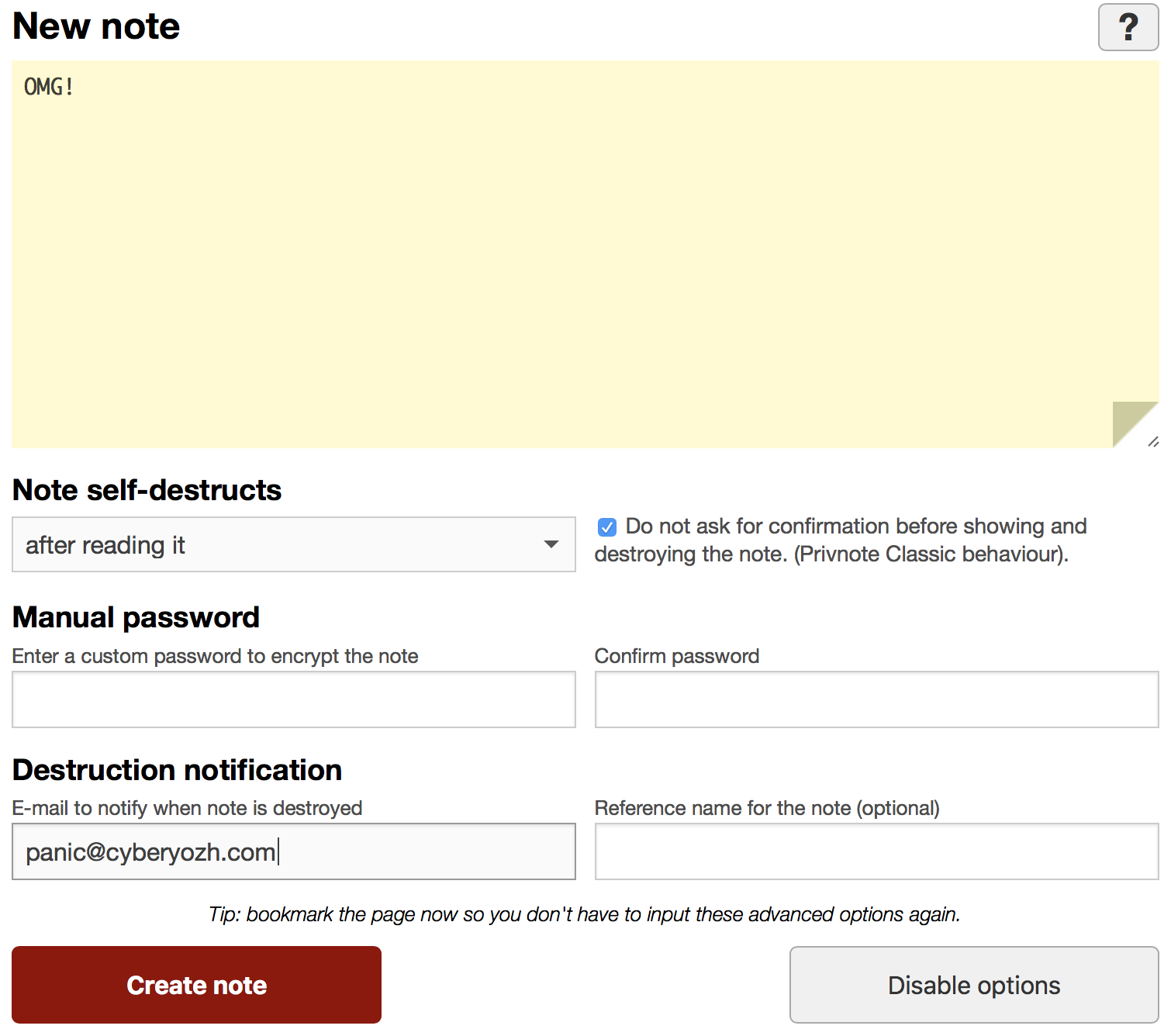
So first, create your privnote. Make sure to select the checkbox “Do not ask for confirmation before showing and destroying the note (Privnote Classic behavior)”, we don’t need any confirmations here.
Enter the email address in the field “Email to notify when note is destroyed”. You will receive an email notification as soon as your note is read. After creating a note, you will receive a link that will resemble something like the following https://privnote.com/a7NEmQCdl#DcieTвk7Sz.
We are not going to send a link to our privnote, instead we will change it, for instance, by using an URL shortener service Bitly. Your link will resemble something like the following https://bit.ly/2JFdYEGeV.
Then you send the recipient a message that contains this link by email, instant messaging or social network. You may want to make your message look tempting for a perpetrator to click the link. For instance, in the following way:
All the papers on the deal currently being made are available here https://bit.ly/2JFdYEGeV. I am waiting for your reply if we need to add some last-minute changes.
The recipient should be notified that this message is bait, otherwise, he or she will click the link setting off the trap. The recipient shouldn’t click the link, it is meant for the secret reader of your correspondence.
Tip
Use a trap to see if someone else is reading your correspondence.Your correspondence can be read by an intermediary, for instance, a social network moderator, and in this case you should change your communication channel or encrypt the data you send. It is much more dangerous when correspondence is read on the sender’s or recipient’s device.
We recommend you set up traps on devices to see if someone else can access them. To protect your information from physical access, take advantage of Panic Button, download and install the application from the official website.
Panic Button is very easy to use: every time a user boots his computer, he deactivates the application performing a special action, for instance, by pressing a key combination or activating a disguised file. A perpetrator is completely unaware of it, and when he accesses your PC, he’s drawn into a trap – Panic Button is activated in logic bomb mode notifying the owner of the computer.
In addition to notifying a user, Panic Button turns off his computer, depending on the settings, deletes browse history, the history of viewed files, pictures, documents. Users can add files to the list of documents that will be destructed by Panic Button to an unrecoverable state upon its activation, preventing a malicious intruder from getting a hold of sensitive data.
During setup, select the option that allows you to send email notifications if Panic Button is activated.
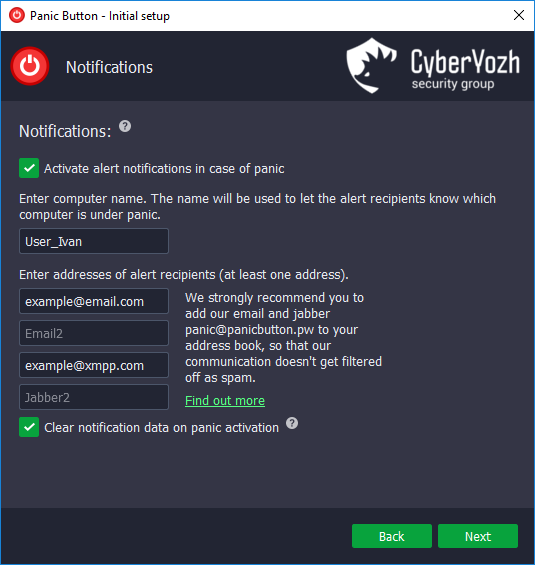
Enable logic bomb.

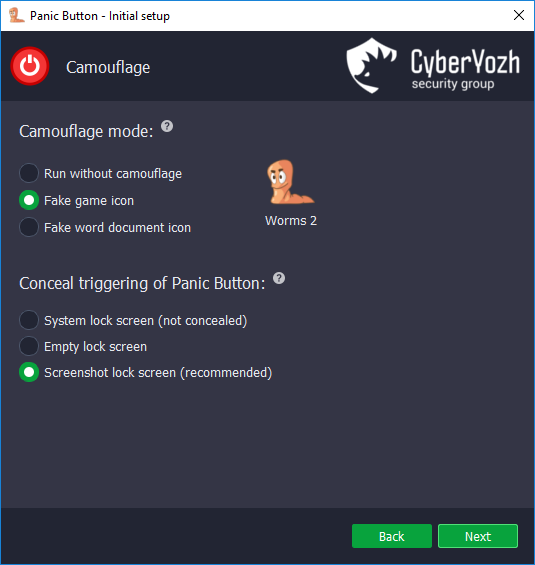
It is recommended that you disguise the application itself.
Tip
Install Panic Button and check if someone else can access your computer.Protection from unsanctioned access is just one of the things Panic Button is designed to do for you. This is a powerful tool for emergency data destruction and protection from forensic analysis, and it will also come handy if someone else accesses your sensitive information.
It won’t be that easy if you are dealing with remote access to your device, for instance, if remote malware (RAT) infiltrated your system. Even in these situations there are different ways to fend off intruders, and you will find out about them in the chapter devoted to malware and the methods of protection from them.
